V3 Sliver C2
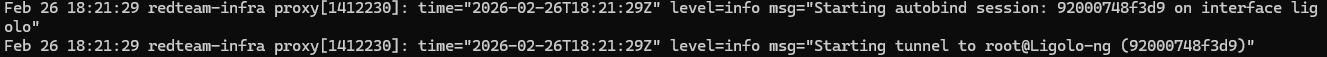
Figure 1: The "Money Shot" — Automated interface binding and routing without touching sudo.
Beyond HTTP: Why I Ditched Cloudflare for V3
In Part II, I set up a serverless redirector using Cloudflare Workers. Don't get me wrong, it worked great for masking the IP. But it had a massive bottleneck: it was stuck at Layer 7.
If I wanted to catch a reverse shell on a weird port or pipe raw TCP traffic, Cloudflare would just drop the connection. I needed a real pipe.
For Version 3, I decided to scrap the serverless layer and go full Layer 3 using Ligolo-ng. But I didn't want to just run it as root like everyone else. The goal was strictly defined: build a fully encrypted tunnel that runs 100% rootless.
Status: Operational / Rootless / Self-Healing
Tech Stack: Ligolo-ng, Linux Capabilities, Systemd, Ansible, AppArmor
The "Senior" Upgrade
Moving from a simple proxy to a full VPN-style tunnel adds complexity. Here is what makes V3 different:
- Total Protocol Freedom: Unlike an HTTP proxy, the TUN interface lets me route any IP protocol to the implant. ICMP, UDP, TCP — it all goes through.
- No Sudo Required: The easy way is to run the proxy as root. I chose the hard way: configuring Linux Capabilities so the service user (`ligolo-svc`) can modify routes without owning the system.
- It Just Works: Connections drop. It happens. I configured the tunnel to auto-detect the specific agent ID and re-bind the network interfaces instantly.
Technical Deep Dive
1. The "Permission Denied" Headache
The biggest OpSec sin in C2 infrastructure is running your proxy as root. If that service gets popped, the attacker owns your entire box. I wanted to run Ligolo as a restricted service user, but there was a catch: creating TUN interfaces and modifying routing tables is a privileged operation.
Instead of giving up and using `sudo`, I leveraged Linux Capabilities. I realized I could grant the binary just the specific "keys" it needed, without giving it the master key to the OS.
# /etc/systemd/system/ligolo-proxy.service
[Service]
User=ligolo-svc
# This was the magic sauce:
AmbientCapabilities=CAP_NET_BIND_SERVICE CAP_NET_ADMIN
CapabilityBoundingSet=CAP_NET_BIND_SERVICE CAP_NET_ADMIN
# Lockdown mode
NoNewPrivileges=true
ProtectSystem=strict
ProtectHome=trueWith this config, ligolo-svc can manipulate the network stack for the tunnel, but if someone breaks out of the process, they can't even list the files in `/home`. Secure by design.
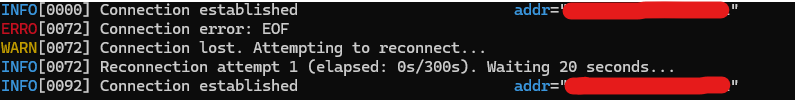
2. Resilience (Or: How I Stopped Worrying and Loved the EOF)
Manual infrastructure is fragile. If the agent drops, you don't want to be waking up at 3 AM to restart a service. I spent a good amount of time debugging the autobind configuration to ensure it persists across restarts.
The screenshot below proves it works. I forced a disconnect (the red EOF error), and the infrastructure didn't panic. It waited 20 seconds, accepted the reconnection, and immediately restored the routing table.
Figure 2: Resilience in action. The proxy takes the hit and recovers the session automatically.
3. Locking Down Sliver
With the tunnel active, my C2 server (Sliver) essentially went "dark." It no longer exposes any ports to the public internet—everything is routed through the tunnel interface.
To take it a step further, I wrote an AppArmor profile that explicitly denies the C2 process from executing `sys_admin` or `sys_module` capabilities. Even if an adversary manages to exploit the C2 binary, they are trapped in a kernel-enforced cage. Overkill? Maybe. But that's the point.
MITRE ATT&CK® Mapping (V3 Update)
Conclusion
Ghost-Sliver V3 was about moving from "scripting" to actual "engineering." Solving the Linux permission issues instead of just running as root was frustrating at first, but the result is an infrastructure that is secure by design, not just by accident.
The combination of Ansible for consistency and Linux Capabilities for least-privilege execution makes this setup ready for actual engagements.
What's Next?
The C2 is automated. The Tunnel is automated. Now I just need to automate the Redirector VPS itself. I'm currently working on a Terraform module to spin up the redirector on-demand, creating a true "One-Click" war room. Stay tuned.