Project: Automated Evilginx2 Infrastructure
Automated Provisioning: From Zero to Phishing-Ready in <3 minutes
Infrastructure as Code: Evilginx2
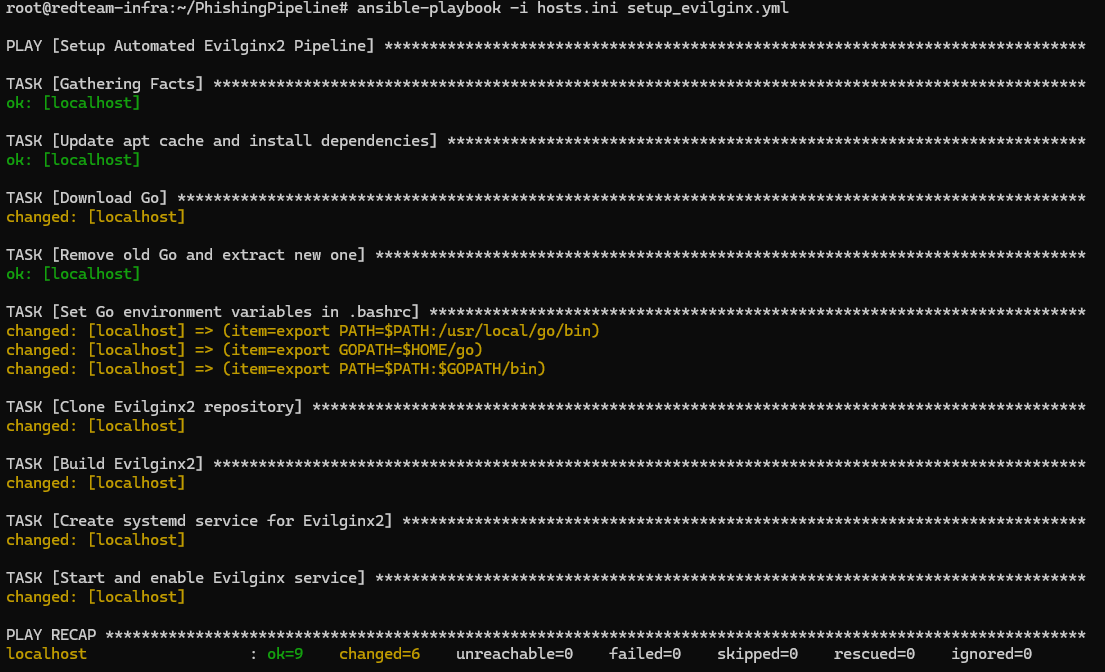
Modern Red Team operations require speed and reproducibility. Manual setup of phishing infrastructure is slow, error-prone, and leaves inconsistent forensic footprints. This project transitions the deployment of Evilginx2—the premier AiTM (Adversary-in-the-Middle) framework—entirely to code.
Goal: Eliminate manual configuration, ensure operational persistence via tmux + systemd, and enable rapid "burn and rebuild" capabilities.
Status: 🟢 Operational
Tech Stack: Ansible, Evilginx 3.3, Go, ARM64/Linux
Operational Advantages
By defining the infrastructure as code (IaC), we achieve:
- Immutable Infrastructure: Every deployment is mathematically identical. No configuration drift.
- OpSec Agility: If an IP is flagged, I can tear down the server and redeploy on a fresh node in under 3 minutes.
- Persistence: Custom systemd units keep the session alive while allowing interactive operator access.
Technical Architecture
1. The Blueprint (Ansible)
The entire environment is defined in a modular Ansible playbook structure. This separates sensitive data (hosts) from the logic (roles).
├── hosts.ini # Target Inventory
├── setup_evilginx.yml # Master Playbook
└── roles/
├── golang-arm64 # Runtime Dependencies
├── evilginx-build # Source Compilation
└── persistence-layer # Systemd & Tmux
2. Advanced Persistence (The Tmux-Systemd Bridge)
Running Evilginx as a background service is standard, but Red Teamers need to see the console to capture live tokens. I engineered a solution where Systemd manages a Tmux session.
The Mechanism:
- Systemd ensures the service auto-starts on boot (persistence).
- Instead of running the binary directly, it spawns a named
tmuxsession. - Operators can SSH in and attach to the session (
tmux attach -t evilginx) to interact with the console, and detach without killing the process.
Tradecraft Acquired
- Enterprise Automation: Translating manual hacking procedures into idempotent Ansible roles.
- Service Orchestration: manipulating Linux init systems (systemd) for offensive persistence.
- ARM64 Optimization: Compiling Go-based attack tooling for cost-effective cloud architectures.
Credits & Disclaimer
This project automates Evilginx2, developed by Kuba Gretzky. It is a tool for authorized security testing and educational purposes only.
Full Documentation
Want to dive deeper into the project? Below is the full report!
📄 Read the Complete Technical ReportIncludes: Infrastructure validation, MFA bypass attempts, and key learnings!